As the festive season unfolds, COIN.HOST is excited to spread the holiday cheer with a special greeting to our valued customers. We deeply appreciate your support throughout the year and want to thank you with a holiday treat!
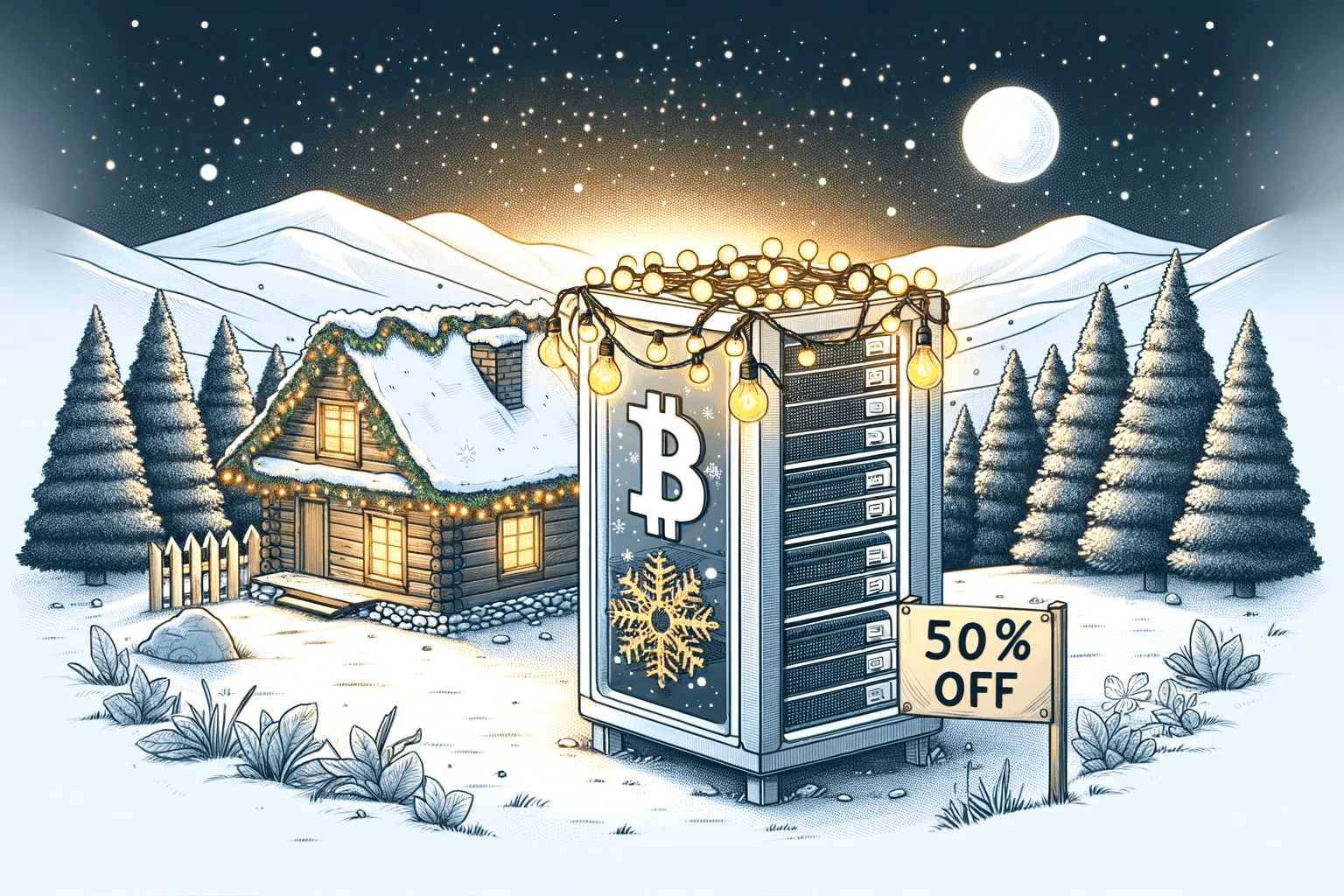
This Christmas and New Year, enjoy a 20% discount on all orders above 50 CHF with the exclusive voucher code: MLNWSWFJID. Whether you’re setting up hosting solutions, upgrading your services, or exploring new features, this is the perfect opportunity to save.
Offer Details:
- Discount: 20%
- Minimum Order: 50 CHF
- Voucher Code: MLNWSWFJID
- Validity: Through January 5, 2025
Take advantage of this limited-time offer and start the new year on a high note with COIN.HOST. Wishing you and your loved ones a joyous holiday season and a prosperous 2025!