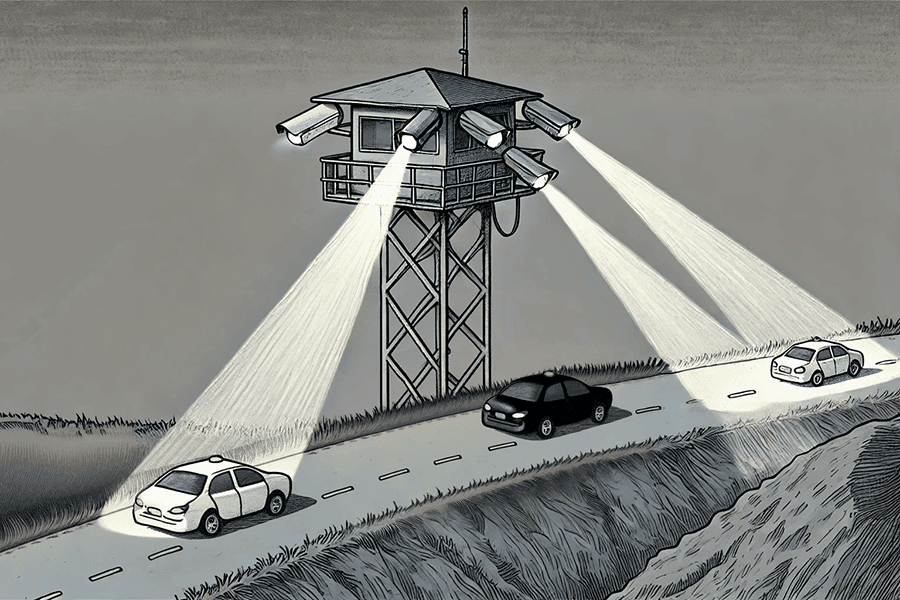
Imagine you are living in a place with strict regulations governing online activity. You wish not only to keep your internet usage private, but also to access resources that are otherwise blocked and obtain information beyond what your government provides. As a result, you decide to use a VPN. However, the authorities remain vigilant for any traffic that appears to originate from a VPN. This is where obfuscated VPN protocols become invaluable. They do more than simply encrypt your traffic, as a standard VPN would: they also disguise it so it does not appear to be VPN traffic at all. In this post, we will explain why this matters, how it works, and the various methods used to achieve it.
Obfuscated VPN Protocols: How They Work and Why They Matter
- By Mia Weston
- In VPN
- [February 14, 2025]